算法分析:XCTF 4th-WHCTF-2017
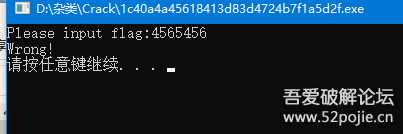
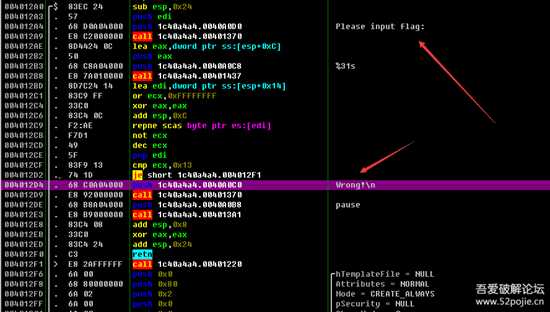
1.下载附件是一个32位无壳console的exe,运行一遍发现基本逻辑就是提示输入一个字符串,输入以后通过一个判断来提示不同内容
image-20220309132114998.png
1
2.既然是exe,那先用OD跑一边
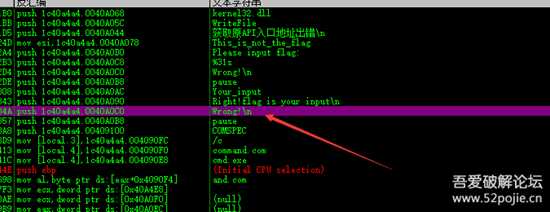
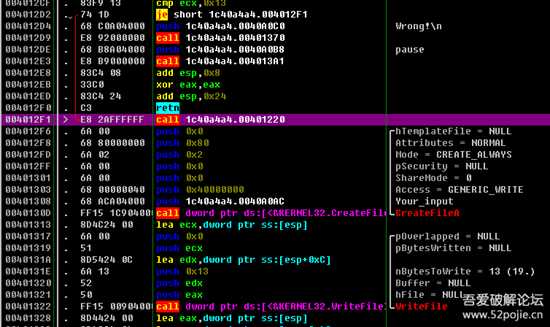
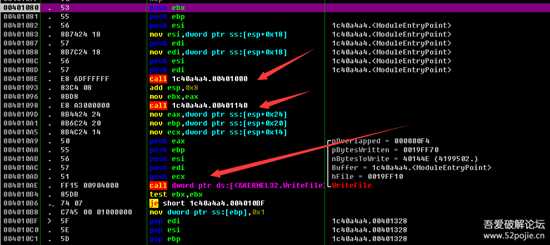
①查看是否有关键字符串
发现关键字符“Wrong!”,这个字符就在我们输入错误后提示的,可以看第一大步的图,双击找到这个字符串的引用(如下图)
image-20220309132505801.png
2
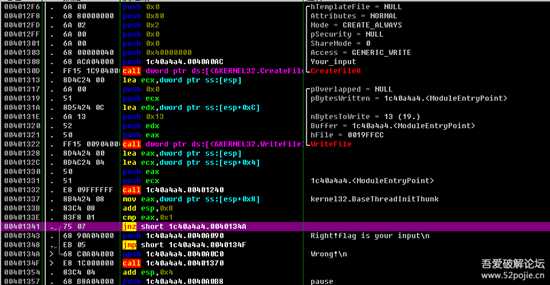
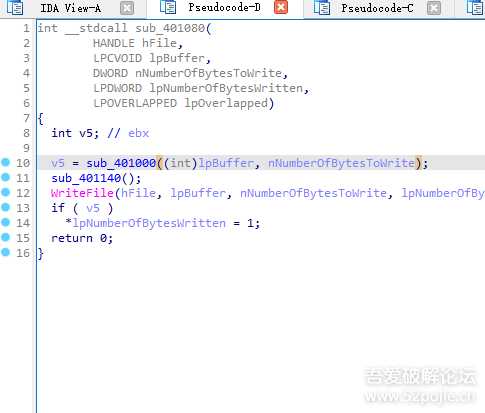
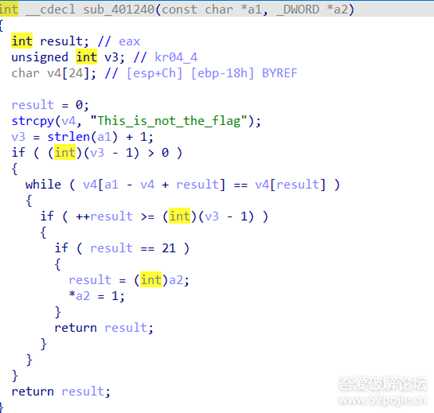
②大概分析引用“Wrong!”的代码段
image-20220309133047232.png
3
发现跳转到输出“Wrong!”函数的jnz在00401341,跳转条件就是eax不等于1,那说明只要eax只要等于1则就不跳转,执行输出“Right!flag is your input”,那现在我们需要做的就是逆推EAX的来源(如上图)
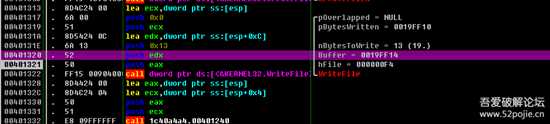
③逆推EAX的来源
00401337 |. 8B4424 08 mov eax,dword ptr ss:[esp+0x8] ; kernel32.BaseThreadInitThunk0040133B |. 83C4 08 add esp,0x80040133E |. 83F8 01 cmp eax,0x100401341 |. 75 07 jnz short 1c40a4a4.0040134A 00401343 |. 68 90A04000 push 1c40a4a4.0040A090 ; Right!flag is your input\n00401348 |. EB 05 jmp short 1c40a4a4.0040134F0040134A |> 68 C0A04000 push 1c40a4a4.0040A0C0 ; Wrong!\n0040134F |> E8 1C000000 call 1c40a4a4.00401370阅读代码可以看到第一步跟踪到的eax是在00401337处被ss:[esp+0x8]赋值,那我们断点到00401337查看ss:[esp+0x8]的值,但是断点运行后居然没停下来而直接判断输出了“Wrong!”,(如下图)
image-20220309133848337.png
4
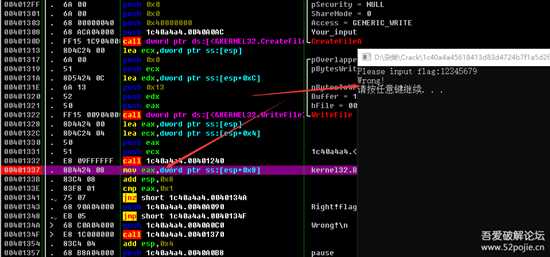
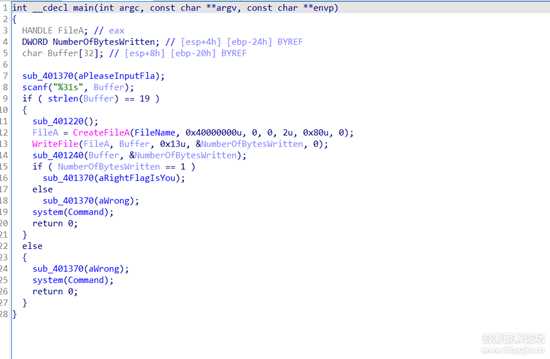
往上浏览代码,发现在004012D4出还有一个Wrong字符串和提示我们输入的信息,那说明这里有有一个初步的对我们输入的判断(如下图)
image-20220309134206340.png
5
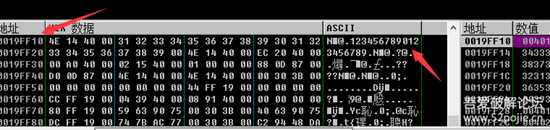
004012A4 |. 68 D0A04000 push 1c40a4a4.0040A0D0 ; Please input flag:004012A9 |. E8 C2000000 call 1c40a4a4.00401370004012AE |. 8D4424 0C lea eax,dword ptr ss:[esp+0xC]004012B2 |. 50 push eax004012B3 |. 68 C8A04000 push 1c40a4a4.0040A0C8 ; %31s004012B8 |. E8 7A010000 call 1c40a4a4.00401437004012BD |. 8D7C24 14 lea edi,dword ptr ss:[esp+0x14]004012C1 |. 83C9 FF or ecx,0xFFFFFFFF004012C4 |. 33C0 xor eax,eax004012C6 |. 83C4 0C add esp,0xC004012C9 |. F2:AE repne scas byte ptr es:[edi]004012CB |. F7D1 not ecx004012CD |. 49 dec ecx004012CE |. 5F pop edi004012CF |. 83F9 13 cmp ecx,0x13004012D2 |. 74 1D je short 1c40a4a4.004012F1004012D4 |. 68 C0A04000 push 1c40a4a4.0040A0C0 ; Wrong!\n004012D9 |. E8 92000000 call 1c40a4a4.00401370004012DE |. 68 B8A04000 push 1c40a4a4.0040A0B8 ; pause004012E3 |. E8 B9000000 call 1c40a4a4.004013A1





 cm.zip2022-3-9 19:49 上传点击文件名下载附件
cm.zip2022-3-9 19:49 上传点击文件名下载附件